RFID As a Service: Core vs. Context
- Blog
- IoT Trends
- RFID As a Service: Core vs. Context
Is the ownership/management/expertise of RFID tags, hardware, associated middleware, and application software core to your company, or is the resulting insight into business operations and decision support that the ensuing location and timely data core to how you run your business?
Looking at an RFID as a Service (RaaS) model through the lens of a business’ core and context activities, we can start to identify how and where RaaS can potentially increase productivity and efficiencies.
In his book, Living On The Fault Line, Geoffrey A. Moore makes the case that companies should solely focus on core activities and outsource all other activities.
“For core activities, the goal is to differentiate as much as possible on any variable that impacts customers’ purchase decisions and to assign one’s best resources to that challenge. By contrast, every other activity in the corporation is not core, it is context. And the winning approach to context tasks is not to differentiate but rather to execute them effectively and efficiently in as standardized a manner as possible.”
In addition, Moore states, “There is no context task that cannot become someone else’s core task.” To the question of why other people can do a better job at a company’s context tasks, Moore’s answer is simple and concise: “this is where they are putting their A team. It’s context to you but is core to them.”
Let’s apply this model to RaaS. The underlying message in Moore’s definition for software applications is that companies can become much more efficient and effective if they focus their internal software deployment on core tasks only, and outsource context software tasks to vendors that specialize in these particular areas. This has a tremendous impact on understanding the dynamic between on-premise software and RaaS applications.
The RaaS model outsources the complexity of generating and maintaining RFID and sensor hardware and software while owning and exercising full control over the information that the system generates, providing the ability to increase the performance of core business activities.
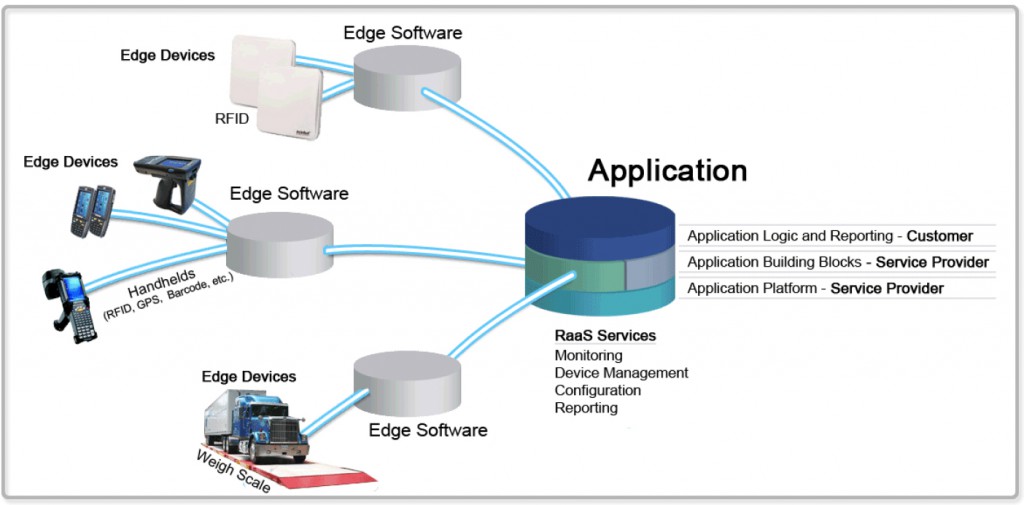
To better understand the relevance of Moore’s insight and how it relates to RaaS, let’s consider the primary components of a RaaS solution and where they fall into the context vs. core paradigm.
RFID, Other Auto-ID Technologies, and Sensors that Perceive the Real World
This is core to hardware vendors and specialists, and in RFID, technological changes are the norm rather than the exception when it comes to tags, readers, antennas etc. For a customer, the hardware is context. Owning the hardware may be core to some customers but even in these situations the deployment and management of it is likely context.
“Edge” Servers and Middleware
Edge servers (typically deployed on-site) filter and aggregate sensor reads to generate useful events (technical events). This process is core to middleware and edge appliances providers, and like their kin on the hardware side, clearly speaks to the need of these best-in-class vendors to keep abreast with the rapidly evolving specter of RFID and sensor technologies, deployment models, integration, standards, and so on. A strong requirement of auto-ID knowledge and pulse adds substance to the argument that the software (in terms of middleware) is a specialized activity that is core to the software provider but clearly context to the end customer.
Applications that Morph Technical Events into Business Events Provide Deep Business Insight
This process and functionality truly generates the new business insight that provides high definition views of product and process and allows a customer to identify and address key pain points. This is an interesting category as the data and event information that these applications serve can provide incredible benefits to the core of a company while again, the application itself — the creation, deployment, and management — is not necessarily core to a company. The value to the customer does not come from core investment in the application layer, rather through intelligent incorporation of specific business logic and the utilization of the mission-critical information and insight these systems provide.
Much of RaaS’ value potential rests in its ability to shift noncore activities to companies who consider them to be core. In addition, RaaS offers a unique value proposition for sensor/RFIDdriven applications. In a RaaS model, the purchase shifts from evaluation to try-before-you-buy (everything) avoiding long, time-consuming evaluation cycles, significantly mitigating technology choice risks while rapidly accelerating time-to-value for the business users.
Other RaaS value drivers include:
1. Instead of inherently expensive application “customization” you take advantage of pre-existing work and infrastructure done by “core-business” companies and simply “configure” your application
2. Instead of relying on internal IT you depend on vendor SLAs
3. Allowing focus on core (integration of business logic, KPIs etc.) aspects of the RFID application and everything else in the application layer and software stack to the RaaS provider.
While this model does fundamentally shift activities and responsibilities, it does not provide any differentiation to the mission of the company. As core as a company might consider RFID application software, one can be sure there’s a qualified SaaS vendor at an equal point if not further along in the learning curve, with the same level of priority, if not greater — as their business is solely dependant on their ability to provide just as an effective alternative to internal development, while making it significantly easier.
Application Core and Context Responsibilities
Consider the example of a RaaS for critical asset location; a “find me” service. This is the type of application commonly used by companies to efficiently locate and track assets within the four walls and beyond. In this model, the service company provides the platform and application building blocks (modeled on similar scenarios). These two components are core to the provider who has incorporated best-of-breed industry processes for finding assets using auto-ID technologies. The customer is now able to leverage the RFID and mobile-enabled “find me” service within the context of their business. By interleaving this service into their business DNA they can start to focus on solving specific pain points associated with locating assets such as reducing maintenance time on a particular field asset by 30% through locating the asset in minutes rather than hours.
Business Logic and Reporting Examples
- What associated information for each asset is necessary?
- What key process indicators (KPIs) and out of tolerance conditions are being tracked?
- What alerts are critical?
- Who has access to information (multiple users, multi-tenancy, and permissions)?
- What is the most effective action that can be taken based on reporting and identified bottlenecks and inefficiencies?
Choosing Qualified Providers
 Again, in choosing the right provider to lay the groundwork and foundation, a company can squeeze the most value out of a solution as possible, and more of their focus can be on the value-driving questions above. Additionally, the provider can assist and lend expertise and experience in these areas as well, as they have developed solutions that are similar in their KPI reporting, alerts preferences and multi-user architecture.
Again, in choosing the right provider to lay the groundwork and foundation, a company can squeeze the most value out of a solution as possible, and more of their focus can be on the value-driving questions above. Additionally, the provider can assist and lend expertise and experience in these areas as well, as they have developed solutions that are similar in their KPI reporting, alerts preferences and multi-user architecture.
The underlying message in applying Moore’s definition to RaaS software applications is that companies can become much more efficient and effective if they focus their internal software deployment squarely on core tasks and outsource their context software tasks to vendors who specialize in that area. It is the incorporation of the customer’s specific business logic and the reporting preferences that should remain core to the business and at the foremost of focus. This methodology falls in line with value propositions that already exist in the RaaS deployments model, and offers a great deal of promise for future adoption trends. Once IT organizations accept this paradigm shift, they will become the productivity heroes to the agile companies of the 21st century.
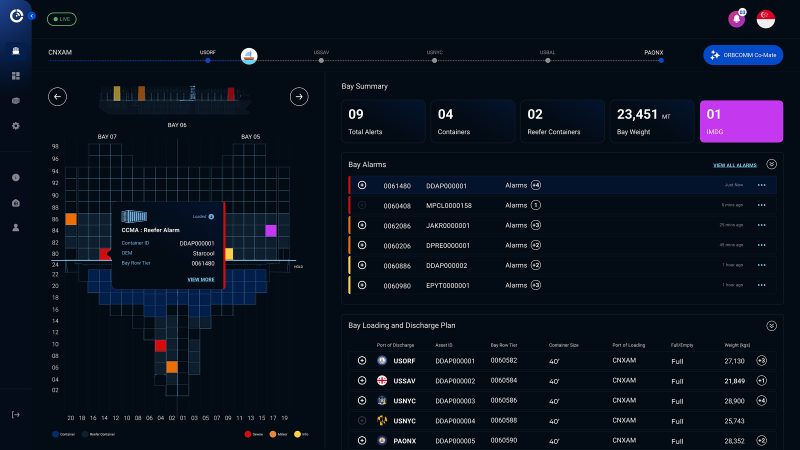
To learn more about ORBCOMM’s scalable RFID solutions from device to dashboard, visit www.orbcomm.com/rfid or email sales@orbcomm.com.
Originally published by RFID Solutions Online